 Today (2014-10-29) the Airspy, was available for pre-order. And I thought that I would do the same thing that I did for the HackRF One. That I would try and keep a track of any questions that I see asked on IRC and the answers given.
Today (2014-10-29) the Airspy, was available for pre-order. And I thought that I would do the same thing that I did for the HackRF One. That I would try and keep a track of any questions that I see asked on IRC and the answers given.I though that I would make a quick log of the problems, queries along with their corresponding solutions and suggestions. And add a few extra notes of my own, if I am able. I have removed all sources of questions and answers to protect peoples privacy (what little is left of it these days).
If you are currently scratching your head, because you have never heard of an Airspy before, then you should probably go to the Airspy website.
I'll probably sort these random questions and answers into some sort of logical order when there is enough of them, Hardware, Software, GNU Radio, RF fundamentals, .... but for now I'll just leave them mixed up higgledy-piggledy in the order that I saw them asked.
Question 1: "External clock input (10 MHz to 100 MHz via MCX connector) – Ideal for phase coherent radios” what is the expected voltage ?
Answer 1: The Clock Input for the Airspy is described on page 5 of the of Si5351C datasheet.
It is 3.3v CMOS voltage levels so, low is below 0.8v (min -0.1v) and high is over 2.0v (max 3.6v). So either a square wave or sine wave that meets this criteria. Almost anything will drive it if the voltage is less than 3.6 V P-P and more than about 2.5 V P-P if it is applied to the CLKIN pin with a series capacitor, a 100k to ground, and a roughly 100k to 3.3 volts.
Extra info 1: So a 0v to 3v square/sine wave at 10MHz would tick all the boxes, and be a good clock source. The Airspy already has a pretty good crystal in it, a 1.5 ppm, low phase noise clock. It may not be perfect for some things but it is a good clock.
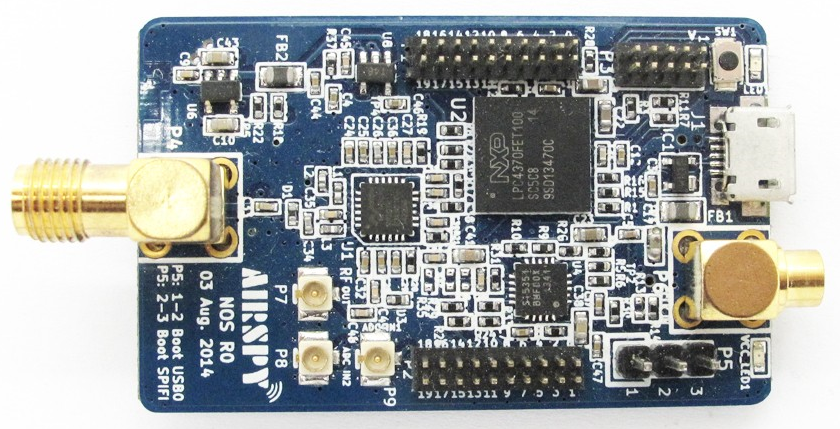
Question 2: "Airspy NOS R0 03 Aug 2014" is written on the PCB silkscreen, what exactly does NOS stand for ?
Answer 2: Nest of Spies.
Question 3: What is the input impedance of the Airspy SMA antenna port ?
Answer 3: 50 ohms
Question 4: What is maximum current that the "4.5v Bias-Tee to pwoer LNA’s and up/down-converters" can use ?
Answer 4: USB 2.0 provides a maximum of 500mA at 5 volts. The Airspy uses less than 400mA at 5 volts (2W), so that would mean that at 4.5 volts in theory the maximum Bias-Tee current would be 111mA (500mW), but there are conversion losses so it is probably closer to 100mA. If more power than this is required then a micro USB Y cable could be used with an external power supply to provide more than 500mA at 5 volts. BiasT LNA's, typically, are at a maximum 250mA for 4.5V (1.125W). So Y cable is probably required, depending on the extra hardware that needs to be powered.
Extra info 4: From http://airspy.com/wp-content/uploads/2014/11/AirSpy_NOS_PinAssignment.jpg the LDO in the Airspy could provide 250mA at 4.5 volts if a Y cable is used to increase the input power. Provided the USB ports on the computer (or external power supply) can provide enough input power.
Question 5: What is the maximum safe input power before you start to damage the Airspy. For example people are breaking the pre-amp in their HackRF One (by enabling it) and pushing more than -5dBm into it (0.1257 volt RMS).
Answer 5: May be 10 dBm (0.7071 Volt RMS) would cause physical damage, for safety stay below 0dBm (0.2236 Volt RMS).
Question 6: What is the input voltage range for ADC IN1(P9) and ADC IN2(P8) ? The LPC4370 datasheet gives the 12-bit ADCHS input as 800mV peak-to-peak in a band from 0 V to 1.2 V. So what is the band, or is the DC offset removed by input circuit and all I need to worry about is the 0.8 volt peak-to-peak ?
Answer 6: 0.8v pp centered around 0.8v
Question 7: There are three gains in the Airspy IF(VGA), Mixer and LNA, what is the best way to use these for optimal results ?
Answer 7: Set the IF(VGA) to 5, the Mixer to 10 and optimize the LNA for the best SNR (the difference between the top of the signal and the noise floor). Then adjust the IF(VGA) so the noise floor stays at -80dBFS, then use the Mixer gain for fine tuning the gain.
Question 8: How do I convert an iq file created by the airspy_rx command into a cfile ?
Answer 8: If we assume that a sample type of "-t 2" (the default) was used with the airspy_rx capture command. Then the following gnuradio flow graph, (similar to the one used by the HackRF One) will convert a default Airspy capture file to a valid cfile.
Question 9: How can I check if my external clock has been selected by the Airspy ?
Answer 9: If you read a document called Si5315 AN619, the answer is hidden within it. You can use the following command "airspy_si5351c -n 15 -r" if bits 2 and 3 are 0 (0x00) then the internal TCXO is active, if bits 2 and 3 are 1 (0x0c) then the CLKIN is active. Or a different register could be used
"airspy_si5351c -n 0 -r". If bit 4 is 0 (0x01) it is locked to an external clock and if it is 1 (0x11) it is not locked to an external clock and is using the internal TCXO.

